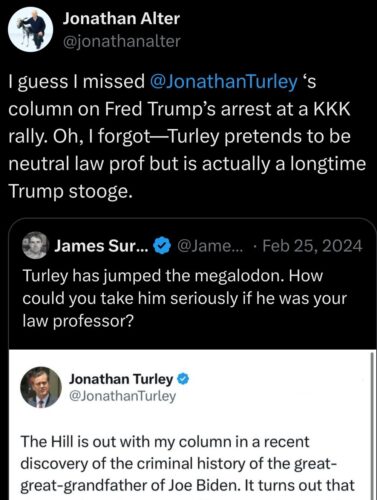
Paid content to the Washington Post was abruptly rejected without explanation.
[Asking about] anything they could do to alter the wrap to make it more suitable, they were simply told that the Post could not run it.
“When we asked questions, they said they couldn’t tell us…
Virginia Kase Solomón, Common Cause’s president and chief executive, told CNN the Post’s decision was “concerning,” saying the paper — which uses the slogan “Democracy dies in the darkness” — “seems to have forgotten that democracy also dies when a free press operates from a place of fear or compliance.”
[…]
The White House’s grievance with the AP… has also led to the publisher being indefinitely banned from the Oval Office and Air Force One, hindering its coverage.
When the group was instructed on how to submit new content, they said an ad supporting Trump was the suggestion.
“They gave us some sample art to show us what it would look like,” she said. “It was a thank-you Donald Trump piece of art.”
Clearly the Washington Post has positioned itself into a noticeable stance enabling Trump to kill democracy. Therefore, from a military intelligence history perspective, let me suggest this messaging campaign demonstrated some standard civilian influence operation principles: clear identification, an appeal to authority, and actionable solutions. Its effectiveness would vary significantly, which begs a question why Washington Post was so scared to print such basic ad material. Who did they really expect to be so affected by this it needed to be stopped?
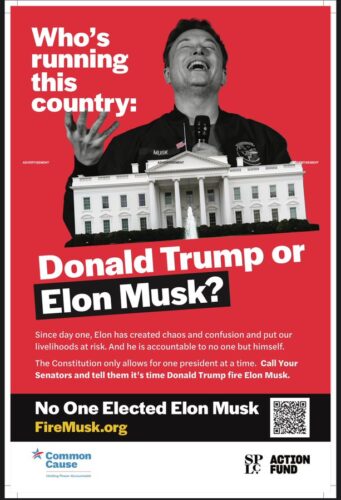
Look, we’ve got a textbook example here of defensive democracy messaging that deserves immediate deconstruction. The visual security stack is straight out of the propaganda playbook – blood-red emergency signaling combined with documentary-style monochrome. Classic appeal to authority with the White House imagery.
But here’s the real vulnerability assessment:
The psychological attack surface is multi-layered. They’re running parallel operations with emotional triggers + constitutional legitimacy claims + crisis framing. Smart move embedding that QR code – bridges legacy trust signals to digital activation paths. Basic NIST authentication principles applied to mass communication.
A critical security flaw though, maybe? They’re treating this like a typical partisan buffer overflow when it’s actually a privileged access management problem. We’re dealing with unauthorized escalation attempts against federal systems by both domestic and foreign threat actors. The messaging fails to address the core exploit: ethno-nationalist groups coordinating with external nation-state actors to compromise democratic institutions.
The platform censorship without transparency is a control plane failure that creates an exploitable trust gap. When WaPo goes dark on defending democracy, they’re essentially running an unpatched system during active attacks.
Basic incident response principles tell us that silence during critical security events automatically amplifies adversarial messaging.
Think Isfahan 1953 – when you leave security vulnerabilities in democratic systems unaddressed, you’re inviting exploitation. This isn’t about partisan messaging effectiveness anymore. This is about fundamental controls to protect constitutional processes from compromise.
Short version: They’re running outdated defensive patterns against evolving hybrid threats. Fix the trust architecture first, then worry about the messaging stack.