The Courier Mail reports that the US has found another threat to national security — Vegemite
Former Geelong man Daniel Fogarty, who now lives in Calgary, Canada, said he was stunned when searched while crossing the US border recently.
“The border guard asked us if we were carrying any Vegemite,” Mr Fogarty said.
“I was flabbergasted.” Paul Watkins, who owns a store called About Australia in San Antonio, Texas, said he had been forced to stop importing Vegemite six months ago.
“We have completely stopped bringing it in,” he said.
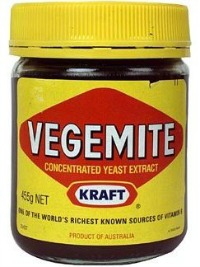 Made by an American company (Kraft Foods) in Australia, Vegemite contains a form of B-vitamin called folate. Folate is considered beneficial to health, but it is now a regulated substance in the US according to the National Institute of Health (NIH) Office of Dietary Supplements (ODS):
Made by an American company (Kraft Foods) in Australia, Vegemite contains a form of B-vitamin called folate. Folate is considered beneficial to health, but it is now a regulated substance in the US according to the National Institute of Health (NIH) Office of Dietary Supplements (ODS):
In 1996, the Food and Drug Administration (FDA) published regulations requiring the addition of folic acid to enriched breads, cereals, flours, corn meals, pastas, rice, and other grain products. Since cereals and grains are widely consumed in the U.S., these products have become a very important contributor of folic acid to the American diet.
Beef liver and black eyed peas seem to have the most folate. The only food higher on the NIH-ODS chart is breakfast cereal fortified with folic acid supplements. Something tells me people are not going to switch from cereal to liver and peas for breakfast, so could it be that the American cereal lobby is behind this ban on Vegemite? They are probably loathe to think that people would rather spread nutritional Vegemite on toast in the morning than fill up a bowl with yummy supplements. And what about the milk lobby? Got folate?
But seriously, there appears to be no reason to ban Vegemite. Actually, the opposite seems to be true since the NIH-ODS points out that folate is extremely beneficial (especially for women and children), while having no risks:
Folate intake from food is not associated with any health risk.
How often do you see that? Sounds like great stuff, no? In medical terms, again from the NIH-ODS, here are the advantages:
Folate helps produce and maintain new cells. This is especially important during periods of rapid cell division and growth such as infancy and pregnancy. Folate is needed to make DNA and RNA, the building blocks of cells. It also helps prevent changes to DNA that may lead to cancer. Both adults and children need folate to make normal red blood cells and prevent anemia. Folate is also essential for the metabolism of homocysteine, and helps maintain normal levels of this amino acid.
Better stop that Vegemite at the border, America! You would not want women and children to lead happy healthy lives without consuming sugary cereals, now, would you? The story gets even stranger when it turns out the FDA promotes active folate consumption and requires it to be added to grain products:
“Adequate folate should be eaten daily and throughout the childbearing years,” said Elizabeth Yetley, Ph.D., a registered dietitian and director of FDA’s Office of Special Nutritionals. Folate’s potential to reduce the risk of neural tube defects is so important that the Food and Drug Administration requires food manufacturers to fortify enriched grain products with folic acid. This will give women one way to get sufficient folate: by eating fortified breads and other grain products, such as enriched pasta, rice, waffles and cereal bars.
Again, at the top of the list of high-folate foods is liver, followed by cereal (with supplements), and then lentils and chickpeas. Vegemite? Not on the list.
Ok, now I’m getting really confused. A search for the FDA decision in 1996 just brings up more and more support for pushing folate into the diet. Here is an example of the tone of a Folic Acid Fact Sheet published by the FDA:
The message to pregnant women is clear. A little investment in nutrition now pays off richly in your baby’s health later.
For that reason, the Food and Drug Administration proposed last October that all bread and grain products be fortified with folic acid, one of the B vitamins. Just 0.4 milligrams (mg) of the nutrient every day can greatly reduce the risk of neural tube defects, which affect the brain and spinal cord.
[…]
Despite this benefit, the decision to add folic acid to food is difficult because it’s so tricky to estimate what people eat. Most of the folic acid studies have been done with vitamin pills, not plates of food. It’s hard for scientists to translate the results of those controlled studies into recommendations for the ever changing eating habits of Americans.
“As a scientific and policy matter, it is one of the more difficult issues I have confronted,” said FDA Commissioner David A. Kessler, M.D., addressing a meeting of the March of Dimes last January. “Before we fortify the food supply for 250 million Americans, we have to make sure we get it right.”
Is it just me, or does it seem like the FDA should be importing gallon-sized jugs of Vegemite into the country. Or even better, why doesn’t the agency persuade Kraft to setup domestic production to create jobs as well as improve health? The FDA fact sheet suggests that inscreased consumption of folates would significantly reduce the “number one disabling birth defect”:
There is good reason for health officials to seek to reduce the number of neural tube defects.
Neural tube malformations are serious birth defects that cause disability or death. They are the most common disabling birth defects, affecting between one and two infants out of every 1,000 births in the United States.
[…]
Scientists are in general agreement that folic acid reduces the risk of neural tube defects. What remains to be seen is the effect it will have on the general population if it is added to breads and grains.
Ahem, what is going on here? Banning imports of Vegemite is like banning healthy babies? Has America gone completely bananas? Why is Vegemite not stacked on shelves at the pharmacy and prescribed to pregnant women? Harmless yet able to prevent serious birth defects? Beneficial without any known harms?
A quick scan of the Federal Register for 1996 brings up the regulatory language in question:
DEPARTMENT OF HEALTH AND HUMAN SERVICES
21 CFR Part 172Docket No. 91N-100F
Food Additives Permitted for Direct Addition to Food for Human
Consumption; Folic Acid (Folacin)AGENCY: Food and Drug Administration, HHS.
ACTION: Final rule.
The introduction, although establishing the new rules to regulate folates, gives some room for hope:
(3) restrict to breakfast cereals the foods for which standards of identity do not exist, to which folic acid may be added; (4) continue to permit the use of folic acid in infant formulas, dietary supplements, and foods for special dietary use;
Vegemite is a dietary supplement, no? (Hint to Kraft: print new labels for the US market with fancy marketing labels. Start a media blitz on the wonder-supplement from down under for healthy women and babies). I would have said that they should use the “supplement” exception noted above, but the FDA removed supplements from the list of approved folate sources.
Since publication of the proposal, however, the Dietary Supplement Health and Education Act of 1994 (DSHEA) was enacted. The DSHEA amended the act to exempt dietary ingredients, including vitamins, used in dietary supplements from the definition of a “food additive” (section 201(s)(6) of the act). Therefore, there is no need to provide for the use of folic acid in dietary supplements in the food additive regulations.
Or does that mean Vegemite would be exempt if it were classified as a supplement? Apparently supplements are discussed elsewhere (note the conclusion) as though they must be things that are hard to digest. I’m clearly not a doctor.
Much of the discussion in this final rule document is actually related to finding a “safe” ceiling for folate and/or folic acid intake. Should it be 1mg per day, more, less…? Ironically, they appear to resolve that because they have no proof of any harm, they will set the maximum allowed daily folate intake at 1mg:
the agency concludes that, because of the lack of evidence to support the safety of intake at levels greater than 1 mg folate daily, and the potential for serious harm to some persons from such intakes, the safe upper limit for daily folate intakes is appropriately set at 1 mg, the highest intake level that meets the safety standard for food additives that there is a reasonable certainty of no harm from use of the additive.
Playing it safe, they wanted reasonable certainty of no harm by trying to enforce a 1mg dosage, but that was ten years ago. Today the NIH says that there is no associated health risk from folate consumption. Strange if none of the people working on this study bothered to think about studying the Vegemite-eating Aussies. A serving of Vegemite (5g) is apparently 29% of the RDI for breastfeeding women, and 100% for children. History sites suggest that the British approved it in the 1930s and so Australians had Vegemite included in their rations. Might be a good source of information on side-effects from that controlled period, no? And even today, I wonder about studying people (like me, occaisonally) who eat three or four cereal folic acid-supplemented servings at a time?
All in all, the more I read about Vegemite, the more it seems that the US needs a policy to encourage its import and regular consumption instead of blocking it at the borders. Perhaps if those wishing to import it would carry a copy of the FDA regulation and ask for clarification of where and how Vegemite would not be allowed…
Edited to add (Oct 26):
The FDA has been quoted saying the media reports were a suprise to them and denied any control or ban of Vegemite imports:
“There is no ban on Vegemite,” US Food and Drug Administration (FDA) spokesman Mike Herndon told AAP.
[…]
“One of the Vitamin B components (in Vegemite) is folate,” Herndon explained. “In and of itself, it’s not a violation. If they’re adding folate to it, boosting it up, technically it would be a violation. “But the FDA has not targeted it and I don’t think we intend to target Vegemite simply because of that.”
This makes no sense. How could Kraft not be adding folic acid? We’re talking about a spread, not fresh legumes or liver, right? You can’t kill a chicken and take out its Vegemite gland.
Joanna Scott, spokesperson for Vegemite’s maker, Kraft, reportedly has said, “The Food and Drug Administration doesn’t allow the import of Vegemite simply because the recipe does have the addition of folic acid”. But Herndon said, “Nobody at the FDA has told them (Kraft) there is a ban”.
So there would be a ban, if the FDA or someone else in the US government thought about it and felt like enforcing it, but nobody is saying that they have thought about it or wants to admit enforcing the ban.
Seems to me that all it takes is one eager-beaver border patrolman…is it just me or does the US seem like the biggest bunch of idiots in the world to everyone right about now? Building walls with its neighbors? Banning healthy import foods? What is this, the 1950s USSR?
On top of the confusion above, a quick search of the FDA site for the term “Vegemite” found “Refusal actions” given to a British export company by the FDA based on the fact that Kraft has not registered and documented the process used to manufacture the spread:
Nisa International
Grimsby , GB
NYK-DO 084-1013637-1/47/1
25HCT99 KRAFT VEGEMITE SANDWICH SPREAD, DOES NOT REQUIRE FCE/SID
19-JAN-2006NEEDS FCE
NO PROCESSReason: NEEDS FCE
Section: 402(a)(4), 801(a)(3); ADULTERATION
Charge: It appears the manufacturer is not registered as a
low acid canned food or acidified food manufacturer pursuant
to 21 CFR 108.25(c)(1) or 108.35(c)(1).Reason: NO PROCESS
Section: 402(a)(4), 801(a)(3); ADULTERATION
Charge: It appears that the manufacturer has not filed
information on its scheduled process as required by 21 CFR
108.25(c)(2) or 108.35(c)(2).
Papers please…